Forcepoint provides cybersecurity solutions focused on data protection, user behavior analytics, and zero trust security, safeguarding organizations globally.
Text Here

Market Leadership:
- Leader in the 2024 Gartner Magic Quadrant for Data Loss Prevention (DLP).
- Strong performer in IDC’s 2024 Worldwide DLP MarketScape.
- Recognized in China IDC’s 2024 Cybersecurity Solutions Report.
- Noted in Forrester’s 2024 Zero Trust Solutions Wave Report.
Video
Data Security Everywhere | Forcepoint
Flagship Products:
Key Features:
|
Key Features:
|

Key Features:
|
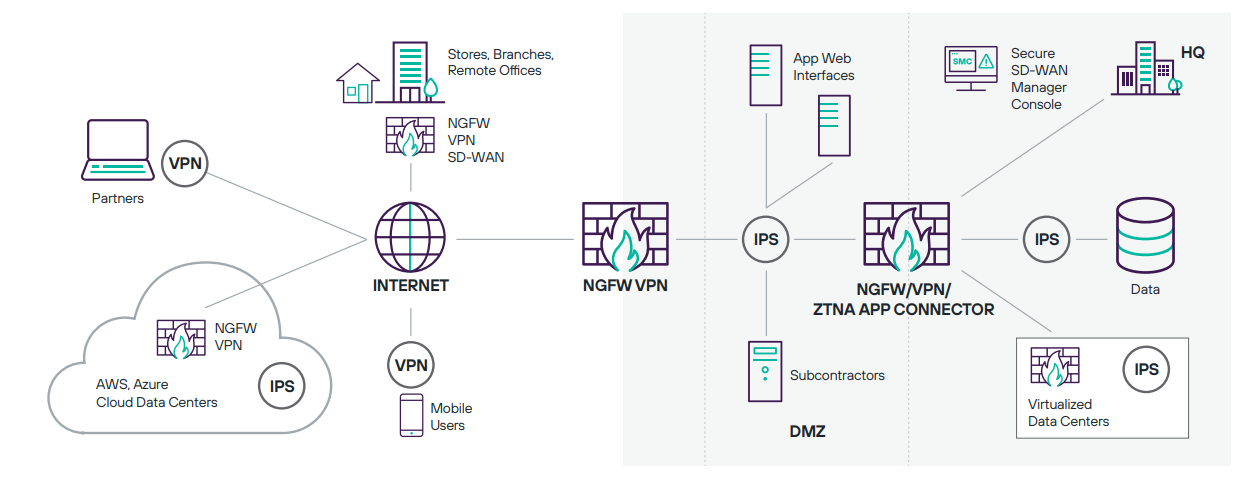
- Forcepoint Next-Gen Firewall: Advanced network security solution.
Key Features:
- SD-WAN integration for optimized network performance.
- Intrusion prevention with deep packet inspection.
- High availability with automated failover and clustering.
- Application-aware policies for granular control.
- Centralized management with real-time analytics.
User Benefits: Forcepoint secures sensitive data, mitigates insider risks, and enables secure access, ensuring operational confidence in a threat-heavy landscape.